As a tech professional, you complete many projects in your career, and some projects leave a lasting impact for some strange and unique reasons. In my career, I have had experience with a project like this, which was a massive project for a blue-chip client. This project despite years of effort and significant investment, never saw the light of day.

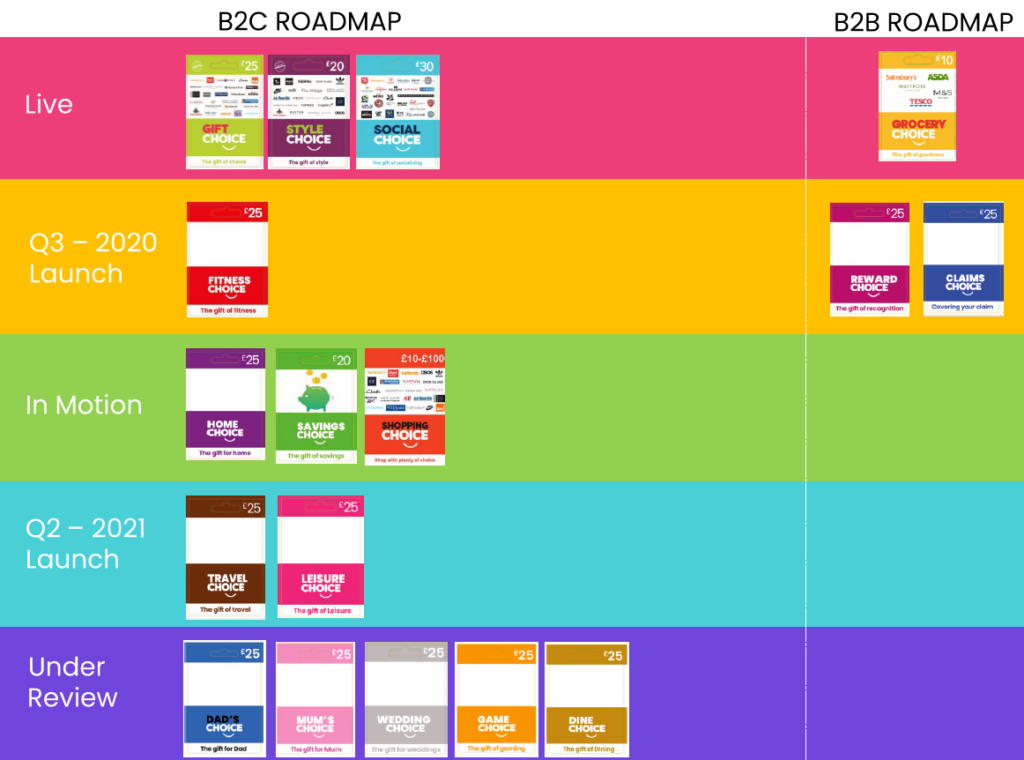
The Idea of a Platform to Revolutionize Dealership Incentive and reward Process
The project was for one of our big blue-chip clients, a well-known name car manufacturing company with hundreds of dealerships across the country.
They needed to build a platform that would connect their dealerships with product information, training materials, incentives, and rewards. The goal was to make things easier for the dealers, help them learn more, and motivate them to sell more. It was a big, exciting project, and we were thrilled to be part of it.
The Development Phase: Ten Months of Hard Work
Our team worked hard for eight months from the vision to build the platform. We made sure it had everything the client wanted. It was designed to be easy to use and packed with features to help dealerships work better. Both our management and development team worked really hard to ensure that every feature met our client’s requirements. The function design covered all the functionalities that could empower dealerships to operate more efficiently, connect to each other, share knowledge and get rewards for their sales. From product selection for rewards to training modules, tracking mechanisms, and reward systems, we completed building the solution within a year of time.
The First Hurdle: IT Restrictions and Access Issues
As we approached the testing phase, we hit the first significant problem. The client’s IT team had very strict rules about who could access their network and hosting environment. For example, setting up a test environment took several months, far longer than anticipated, as we had very limited input in the process. Once the servers were ready, the most frustrating challenge was getting a daily token to access the server where we were supposed to host the staging version of the platform. Every morning, we had to put in a request to their IT team for access to the servers, and by the time it was granted, half the day was already gone. As they did not have any automated process to raise a ticket, we had to email a shared email address to get a token. This delay slowed down our process dramatically and tested our patience. We suggested setting up a staging environment in our infrastructure that could speed up the process, but the client wanted to host everything within their servers. In the end, it took over 6 months to complete the staging part.
Staging to Live: More Restrictions, More Delays
After overcoming many many challenges, we finally completed the user acceptance testing in their staging environment. And we were ready to set up the live environment. However, this process brought even more restrictions. The client’s IT team had additional security procedures that further delayed the access to the live environment. What should have been a simple and quick process turned into a months-long struggle. After several months of meetings and discussions, we finally got access to the live servers, and we started setting up the platform. Even though we had the same difficulties of getting server access permission every day, we managed to set up everything as quickly as we could.
The Final Blow: A Corporate Move and Changing Priorities
Just as we were planning and getting ready to launch the platform, the client dropped a bombshell: their headquarters was relocating to a new location. The live environment was within a data centre of our client’s headquarters, and the moving of the headquarters meant that the launch had to be postponed. The client’s IT team had to work with the logistics of the move, prioritising their core platforms to remain operational during the transition. Even though it was initially expected to be completed within 6-8 months, it stretched into more than two years. During these 2 years, the project was updated many times to accommodate some new requirements and went through a few other changes.
The Cost of Delay: Over Half a Million Pounds and Counting
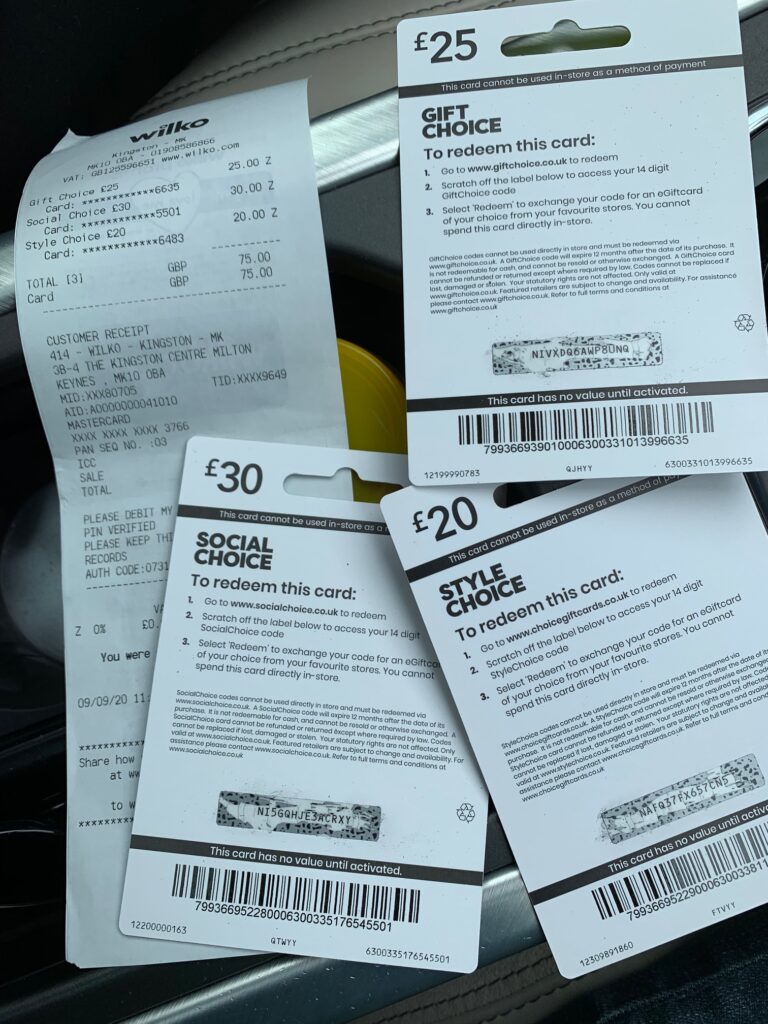
By this point, the development cost of the project had already reached over half a million pounds. On top of that, our company was paid over another quarter million pounds to manage and maintain the platform during the two-year delay. A third-party company was also involved in supplying physical pre-paid master cards that were branded for our client. We ended up with hundreds of Mastercards with our client logo on them but could not use them for anything else. It was a tremendous amount of money, and the platform, which could have helped the client so much, was sitting there, unused.
The End of the Road: A Change in Leadership and a Scrapped Project
After nearly four years(1 year of development, 1 year of modification, testing and setting up a live environment and 2 years of hibernation with some modification), the client underwent a change in leadership. The project’s cost was over a million pounds by that time. The new stakeholders, who had not been involved in the project’s development, took another 6 months to review the platform and decided that it no longer aligned with their vision. Even though the product was fully developed and ready to launch, the project was scrapped. The decision to scrap the project was very hard to digest for us. After five years of hard work, countless challenges, and a significant financial investment, the project was finally thrown to the bin without ever going live.

Lessons Learned and Lingering Questions
This unusual experience taught me some important lessons. A fully built, working platform that was thrown away after nearly five years showed me how crucial it is to have clear goals and the ability to adapt when things don’t go as planned. The final decision left me feeling disappointed as I believed the project had a lot of potential that was wasted. I could not understand how a company could spend so much money and time on something and walk away without getting anything out of it. And it also made me wonder how big companies could afford to spend so much without making sure the project would actually be useful in the end.
Even though the platform never went live, I hope the lessons I learned will help me in future projects. After all, even failed projects can teach us something valuable. As for the client, I can only hope they find some way to use the product, even if it’s for something different than originally planned.